The North Korean Konni APT is running a multi-stage campaign that uses spear-phishing to deploy EndRAT, then abuses the victim’s KakaoTalk desktop application to propagate malware laterally through trusted contact networks. The operation combines long-dwell persistence, multi-RAT redundancy (EndRAT, RftRAT, Remcos), and social engineering via human rights-themed lures — making compromised individuals active nodes in the attack chain. Security teams face a compounding threat where initial containment does not stop secondary propagation already in progress.
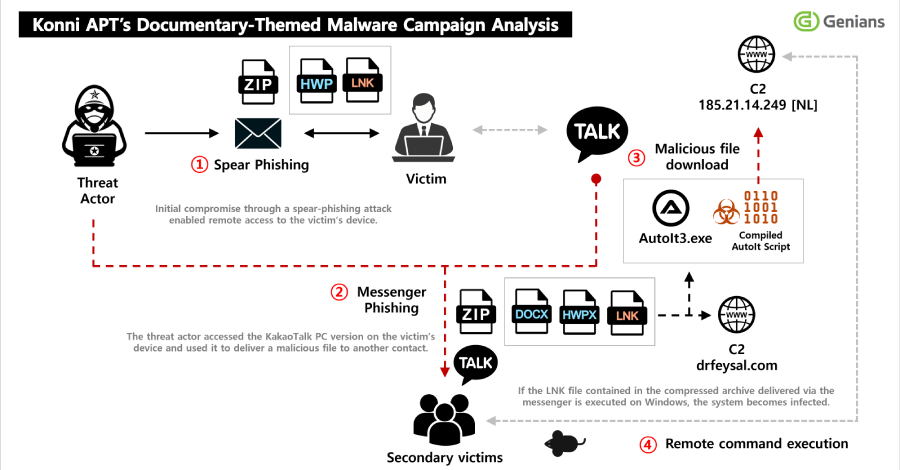
Konni’s latest campaign demonstrates a deliberate shift from endpoint compromise to network-of-trust exploitation. The initial vector — a spear-phishing email posing as a North Korean human rights lecturer appointment notice — reflects careful target selection. The lure is credible within the South Korean civil society and policy research community, where recipients would have reason to expect such correspondence. The ZIP attachment delivers a Windows LNK file that executes a staged infection chain: remote payload retrieval, scheduled task persistence, decoy PDF display, and final EndRAT installation. This execution pattern is designed to minimize suspicion at each step, giving the operator time to establish a foothold before detection.
EndRAT, written in AutoIt, provides core RAT capabilities: file management, remote shell, data transfer, and persistence maintenance. Its use of AutoIt is operationally significant — AutoIt-compiled binaries have historically evaded signature-based detection and can be rapidly recompiled to defeat hash-based blocklists. The presence of RftRAT and Remcos RAT artifacts on the same infected host signals that Konni assessed the victim as high-value and deployed redundant access mechanisms. If one RAT is detected and removed, the others maintain operator access. This multi-RAT strategy is a deliberate resilience measure, not opportunistic overlap.
The KakaoTalk propagation mechanism is the most operationally novel element. After establishing persistence, the actor accessed the victim’s installed KakaoTalk desktop client and selectively sent malicious ZIP files to contacts from the victim’s friend list. File names mimicked North Korea-related educational content, maintaining thematic consistency with the original lure. This converts the compromised endpoint into a trusted relay — recipients receive malware from a known contact, bypassing the skepticism a cold phishing email would trigger. Genians documented a precedent for this tactic in November 2025, when Konni used signed-in KakaoTalk sessions to distribute payloads while triggering remote Android device wipes via stolen Google credentials. The current campaign refines that approach by pairing it with a new RAT family and more targeted contact selection.
From a threat intelligence standpoint, the dwell time reported by Genians is a critical indicator. Extended, undetected persistence on the initial victim’s host is what enabled the KakaoTalk propagation phase — the actor needed time to identify valuable contacts and craft contextually appropriate filenames. This suggests Konni’s operational tempo prioritizes reconnaissance and relationship mapping over rapid exfiltration. Security teams investigating any Konni-related IOC should treat the infected endpoint as a secondary source node, not just a victim, and audit outbound KakaoTalk communications retroactively. The single-source nature of this reporting (Genians Security Center) means some technical details — particularly full IOC sets, C2 infrastructure specifics, and precise dwell time figures — have not been independently corroborated at this time.
- Takeaway 1: Audit KakaoTalk desktop application activity on any host flagged for Konni indicators — outbound file transfers to contacts may mean secondary victims have already been seeded before containment began.
- Takeaway 2: Block or alert on AutoIt-compiled executables in enterprise environments; EndRAT’s AutoIt basis is both a detection gap and a recompile-to-evade risk that signature-only controls will miss.
- Takeaway 3: Multi-RAT deployment (EndRAT + RftRAT + Remcos) on a single host is a high-confidence signal of high-value target designation — treat any confirmed Konni infection with multi-RAT artifacts as a priority incident requiring full forensic scope, not standard malware remediation.
- Takeaway 4: Scheduled tasks remain Konni’s persistence mechanism of choice — hunt for tasks created around the time of suspected LNK execution, particularly those invoking scripting interpreters or AutoIt binaries from user-writable paths.
- Takeaway 5: Organizations in South Korean civil society, human rights advocacy, or North Korea policy research should treat unsolicited appointment or speaking-role notifications as high-risk lure categories and enforce attachment sandbox policies accordingly.