The GlassWorm campaign is executing a broad, multi-platform supply-chain attack targeting developers by compromising 72 Open VSX extensions, 151 GitHub repositories, and multiple npm packages. The operation exploits VS Code’s native extensionPack and extensionDependencies mechanisms to convert trusted, previously benign extensions into malware delivery vehicles, abusing developer trust rather than breaking it. The downstream risk extends beyond individual developers to any enterprise environment where affected toolchain components reach production pipelines.
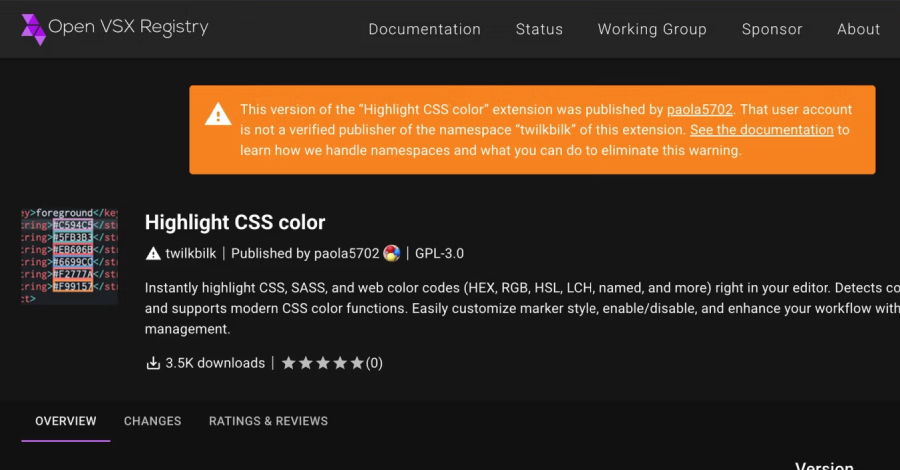
GlassWorm represents a calculated escalation in developer-targeted supply-chain attacks. The campaign does not rely on creating new malicious extensions from scratch. Instead, it compromises existing, trusted Open VSX extensions and then exploits VS Code’s extensionPack and extensionDependencies metadata fields to pull in additional malicious components during normal extension installation or update cycles. This technique is significant because it subverts the trust relationship developers have already extended to legitimate packages, the initial extension may pass cursory review while the dependency chain delivers the payload.
The scale reported, 72 Open VSX extensions and 151 GitHub repositories, suggests an automated or semi-automated compromise process rather than manual, targeted intrusion. The acceleration noted in early March 2026 indicates the campaign moved from initial staging to active deployment within a short operational window. The simultaneous targeting of npm packages alongside VS Code extensions broadens the attack surface considerably, potentially affecting build pipelines and CI/CD environments that consume both ecosystems. Security teams should treat this as a toolchain-wide compromise, not an isolated IDE plugin issue.
The abuse of extensionPack and extensionDependencies is technically notable. These VS Code mechanisms are designed for legitimate bundling of related tools, and many developers and security scanners do not scrutinize transitive extension dependencies with the same rigor applied to direct installs. An attacker who controls a parent extension in a trusted pack can introduce malicious child extensions that install silently. This mirrors transitive dependency abuse seen in npm and PyPI supply-chain attacks, now applied to the IDE layer, a surface that has historically received less automated scanning attention.
From a threat intelligence perspective, the multi-platform coordination across Open VSX, GitHub, and npm points to a threat actor with operational maturity. Maintaining compromise across three distinct ecosystems simultaneously requires either multiple access vectors or a centralized infrastructure with broad repository access. The GitHub repository compromise component is particularly concerning because it may affect source-level artifacts, meaning malicious code could be introduced upstream of package publication, complicating detection efforts that focus on published package contents alone.
One significant gap in available reporting is the absence of specific IOCs: no confirmed malicious extension names, no identified npm package identifiers, no C2 infrastructure details, and no confirmed payload type or post-compromise behavior are available from the single source. Security teams cannot yet build targeted detection rules from published indicators. Until IOCs are released, detection strategy must focus on behavioral controls: monitoring for unexpected extension installations, auditing extensionPack dependency graphs, and flagging outbound network connections from IDE processes. The lack of corroborating sources also means the full scope, 72 extensions, 151 repositories, should be treated as a working figure pending independent confirmation.
- Audit your VS Code extension inventory now: review extensionPack and extensionDependencies metadata for all installed extensions, including those sourced from Open VSX, and flag any transitive dependencies not explicitly approved.
- Treat IDE plugins as part of your software supply chain: apply the same dependency scrutiny to VS Code extensions that you apply to npm or PyPI packages, transitive extension installs can deliver malicious payloads without user confirmation.
- Block or monitor outbound connections from IDE processes at the network perimeter: until specific IOCs are published, behavioral detection of unexpected IDE-sourced network traffic is the most actionable control available.
- Inventory GitHub repository dependencies in your CI/CD pipelines: the 151 compromised repositories may include source-level artifacts consumed during build; validate the integrity of any external GitHub-sourced code used in automated pipelines.
- Do not wait for vendor-published IOC lists before acting: the absence of specific malicious package names in current reporting means proactive environment hardening, extension allowlisting, pipeline integrity checks, is the primary defensive posture until detailed indicators are available.