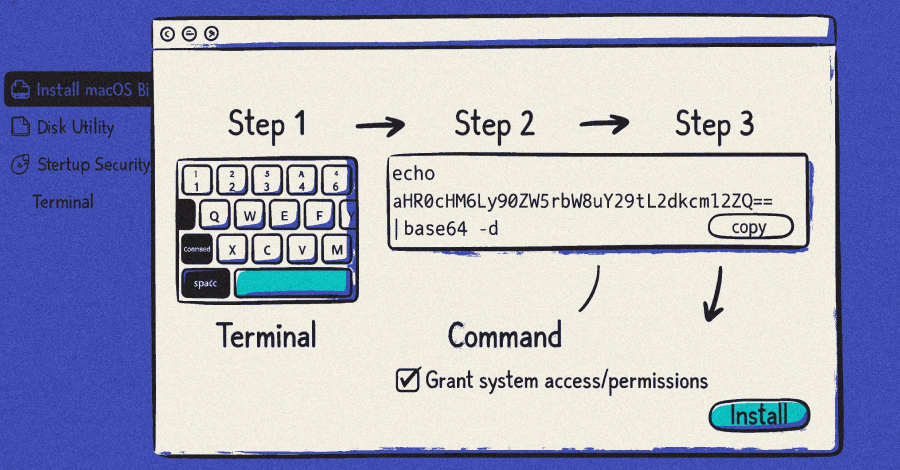
Three distinct ClickFix campaigns between November 2025 and February 2026 deployed the MacSync macOS infostealer by impersonating legitimate AI tools, including ChatGPT and Claude Code, tricking users into executing malicious terminal commands. The technique has expanded into a broader ecosystem spanning at least 20 AI-tool-lure campaigns in 30 days, 250+ compromised WordPress sites across 12 countries, and multiple malware families targeting both macOS and Windows. Developers are the primary target population: the curl-pipe-shell installation pattern they already trust makes malicious commands difficult to distinguish from legitimate ones.
The MacSync campaigns documented by Sophos represent a deliberate, iterative development cycle rather than a static malware deployment. The November 2025 campaign used a fake Google Sites page impersonating ChatGPT Atlas browser installers. By December, operators shifted to abusing legitimate OpenAI ChatGPT shared conversation URLs to add perceived authenticity before redirecting to malicious GitHub-themed landing pages. The February 2026 variant introduced dynamic AppleScript payloads and in-memory execution, eliminating static artifacts that endpoint tools can detect. This three-month trajectory shows a developer actively hardening the payload against macOS security improvements and behavioral detection engines. The in-memory execution approach in particular complicates incident response by leaving minimal forensic evidence on disk.
The targeting rationale documented by Pillar Security is operationally important: macOS users in developer roles carry high-value credential stores including SSH keys, cloud provider tokens, and cryptocurrency wallet seed phrases. MacSync targets all of these simultaneously — keychain databases, credentials, files, and seed phrases — making a single successful compromise potentially worth significant follow-on access. Pillar Security observed at least 20 distinct campaigns targeting AI and vibe coding tools between February and March 2026, with seven campaigns exclusively targeting macOS and nine targeting both platforms. The AI-tool lure category works precisely because the developer population it targets routinely installs tools via copy-pasted terminal commands. Homebrew, Rust, and nvm all use the curl-pipe-shell pattern legitimately, which is the social cover that makes InstallFix effective where traditional ClickFix had to manufacture urgency through fake CAPTCHAs or error screens.
The KongTuke traffic distribution system (also tracked as 404 TDS, Chaya_002, LandUpdate808, and TAG-124 per Trend Micro) represents a parallel and more enterprise-focused threat track within the same ClickFix ecosystem. KongTuke injects malicious JavaScript into compromised WordPress sites to deliver ModeloRAT via PowerShell, and its CrashFix variant delivers malicious browser extensions instead of direct command execution. Critically, Trend Micro notes that ModeloRAT checks whether a system belongs to a corporate domain and identifies installed security tools before continuing execution — this is targeted behavior consistent with initial access brokering or ransomware precursor activity, not opportunistic credential harvesting. The use of DNS TXT records to stage PowerShell commands adds another layer of detection complexity since DNS-based command retrieval evades many network inspection tools focused on HTTP/HTTPS.
The Rapid7-documented WordPress compromise campaign, active since December 2025, adds significant scale context: over 250 infected websites across 12 countries, including regional news outlets and local businesses, are serving ClickFix lures impersonating Cloudflare human verification challenges. The four malware families observed in this campaign — StealC, an improved Vidar Stealer variant, Impure Stealer (.NET), and VodkaStealer (C++) — indicate either multiple operators purchasing access to the same compromised site infrastructure or a single operator running parallel payloads. The WordPress infection vector remains unconfirmed but Rapid7 attributes it to plugin/theme vulnerabilities, stolen admin credentials, or exposed wp-admin interfaces. This gap in attribution matters operationally: defenders cannot prioritize patching without knowing which vector is active.
Across the full campaign landscape, one structural pattern stands out: legitimate platforms are being weaponized as trust proxies. ChatGPT shared conversations, Google Sites, GitHub-themed pages, Cloudflare Pages, and Squarespace all appear in the delivery chain. This is not incidental — operators are deliberately inserting recognizable, trusted brand surfaces between the initial lure and the malicious payload. Security awareness training that teaches users to trust HTTPS or recognize known domains provides no protection against this pattern. Detection must occur at the command execution layer, not the URL inspection layer.
- Block or alert on terminal/PowerShell commands spawned from browser processes — this is the execution chokepoint across all ClickFix variants including MacSync, InstallFix, KongTuke, and CrashFix.
- MacSync’s February 2026 variant uses in-memory AppleScript execution with no on-disk payload artifacts; endpoint tools relying on file-based detection will miss it — verify your macOS EDR covers in-memory behavioral detection.
- Audit and rotate SSH keys, cloud tokens, and API credentials for any macOS user who installed developer tools via copy-pasted terminal commands between November 2025 and present — MacSync specifically harvests these alongside keychain and crypto wallet seed phrases.
- WordPress site administrators should treat exposed wp-admin interfaces as a critical risk given 250+ confirmed compromises across 12 countries; enforce 2FA on admin accounts, audit for unknown administrator accounts, and patch all plugins and themes immediately.
- KongTuke’s ModeloRAT performs corporate domain checks and security tool enumeration before executing — treat any ClickFix-derived infection in a corporate environment as a potential targeted intrusion, not opportunistic malware, and escalate to full incident response.
- Developer onboarding documentation and internal wikis should explicitly warn that legitimate tools (Homebrew, Rust, nvm) use the curl-pipe-shell pattern — and that malicious commands are designed to look identical — since this population is the primary target of AI-tool lure campaigns.