Storm-2561 has run a sustained SEO poisoning campaign since at least May 2025, redirecting enterprise users searching for legitimate VPN clients to attacker-controlled sites that deliver digitally signed trojanized installers. The campaign deploys the Hyrax information stealer via DLL sideloading, captures VPN credentials through a fake sign-in prompt, and uses GitHub as a trusted delivery channel. Microsoft observed the latest iteration in mid-January 2026 and has since taken down the repositories and revoked the signing certificate, but the underlying playbook remains operational risk.
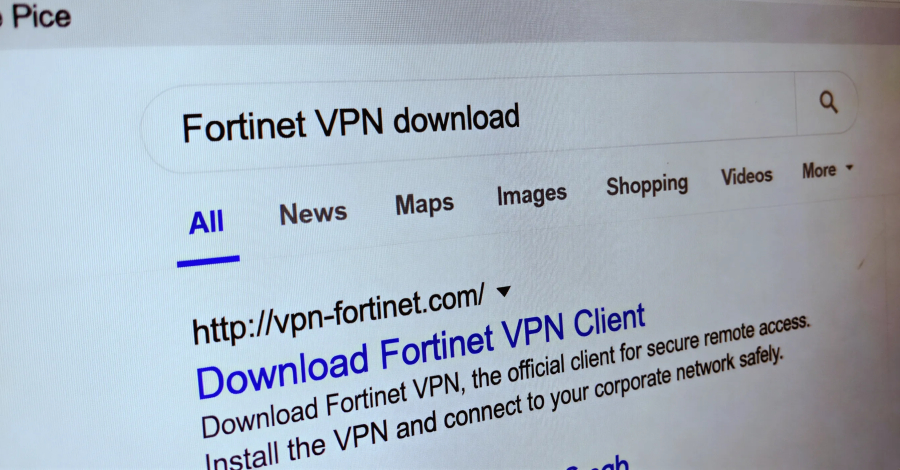
Storm-2561 has refined a multi-stage trust exploitation chain that is more effective than traditional phishing precisely because it intercepts users at the moment they are actively seeking legitimate software. By manipulating Bing search rankings, the threat actor positions malicious sites in front of users who already have intent, employees looking to install or update enterprise VPN clients from vendors including SonicWall, Ivanti (formerly Pulse Secure), and Hanwha Vision. This removes the need to manufacture urgency or lure victims through unsolicited contact. The user initiates the action themselves, which also reduces suspicion and bypasses user awareness training that focuses on inbound phishing vectors. (Sources: Microsoft Threat Intelligence, Cyjax, Zscaler)
The technical execution layer is deliberately designed to defeat endpoint and supply chain controls. Installers arrive as ZIP files containing MSI packages. During installation, the MSI sideloads malicious DLL files, a technique that abuses the Windows DLL search order to execute attacker code under the context of a trusted process. The malware components carry a valid digital signature attributed to ‘Taiyuan Lihua Near Information Technology Co., Ltd.,’ which Microsoft has since revoked. Signed malware bypasses signature-based detection and may suppress security warnings during installation. Persistence is established via the Windows RunOnce registry key, ensuring execution survives reboots without requiring more conspicuous persistence mechanisms. (Source: Microsoft Threat Intelligence)
The credential harvesting mechanism is behaviorally convincing. After installation, the trojan presents a fake VPN sign-in dialog that closely mimics the legitimate client interface. When the user submits credentials, the malware displays a generic error message and redirects to the authentic VPN vendor site, a deliberate misdirection that makes the interaction feel like a routine login failure rather than a compromise event. VPN credentials harvested this way provide direct network access, making them substantially more damaging than general account credentials. Depending on the target environment, a stolen VPN credential combined with the absence of MFA could represent complete perimeter bypass. (Source: Microsoft Threat Intelligence)
The campaign’s use of GitHub as a file hosting intermediary is a calculated trust transfer. GitHub’s reputation causes many endpoint security products, web proxies, and user instincts to treat downloads from the platform as lower risk. This is not a novel technique, GitHub and similar developer platforms have been used repeatedly for malware staging, but it remains effective because blocking GitHub broadly is operationally disruptive for most enterprises. Microsoft’s takedown of the attacker repositories addresses the specific infrastructure, but Storm-2561 has demonstrated operational continuity across multiple iterations since May 2025, with documented pivots from Bumblebee loader delivery (Cyjax) to Ivanti-specific credential theft (Zscaler, October 2025) to the current Hyrax-based campaign (Microsoft, January 2026). Infrastructure takedown slows but does not neutralize a threat actor with an adaptable playbook.
One analytical gap in the available reporting is the downstream use of harvested credentials. Microsoft characterizes Storm-2561 as financially motivated, but none of the three documenting organizations (Cyjax, Zscaler, Microsoft) have published evidence of how stolen VPN credentials are monetized, whether through direct network intrusion, sale on criminal markets, or use in follow-on ransomware operations. That attribution to financial motivation is plausible given the credential-focused tooling, but the full kill chain post-exfiltration remains unconfirmed in public reporting. Security teams should treat any Storm-2561 indicator as a potential precursor to broader network compromise, not a contained credential theft event.
- Enforce MFA on all VPN and remote access accounts immediately, harvested VPN credentials are useless against accounts protected by phishing-resistant MFA (FIDO2/hardware token preferred). This is the single highest-ROI control against this specific campaign.
- Audit software download policies: employees should obtain VPN clients exclusively from internal distribution channels, vendor portals accessed via bookmarked URLs, or IT-managed deployment systems, never from search engine results. Update acceptable use and endpoint provisioning policy to reflect this explicitly.
- Hunt for DLL sideloading indicators and RunOnce persistence entries on endpoints where VPN clients were recently installed outside approved channels. Look for unsigned or anomalously signed DLLs loaded by VPN client processes, and audit HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce for unexpected entries.
- Block or monitor downloads from GitHub and similar code hosting platforms at the proxy layer for executable content types (ZIP, MSI, EXE). If broad blocking is not feasible, alert on MSI/ZIP downloads from github.com/raw.githubusercontent.com originating from non-developer workstations.
- Threat intelligence teams should monitor for new infrastructure associated with Storm-2561, particularly domains mimicking enterprise VPN vendors (pattern: [vendor-name]-vpn[.]org, [vendor-name]-client[.]com). The actor’s history shows rapid infrastructure replacement after takedowns.