A suspected Chinese state-sponsored threat cluster designated CL-STA-1087 has conducted sustained espionage operations against Southeast Asian military organizations since at least 2020, deploying custom backdoors AppleChris and MemFun alongside a modified Mimikatz variant to extract military intelligence. The campaign prioritizes precision collection of command, control, communications, computers, and intelligence (C4I) data and information on joint Western military collaboration rather than bulk data theft. The malware’s use of dead drop resolvers, modular payload delivery, and process hollowing makes detection difficult and gives defenders limited time to act before the actor achieves deep persistence.
CL-STA-1087 represents a textbook long-game espionage operation. Unit 42 researchers identified the cluster after detecting suspicious PowerShell execution configured to sleep for six hours before establishing reverse shells, a deliberate technique to outlast behavioral monitoring windows. The initial access vector remains unconfirmed, which is itself a significant intelligence gap. Without knowing how the actor gains a foothold, defenders cannot close the entry point; hunting for post-exploitation artifacts is a secondary defense that compensates for a missing primary one.
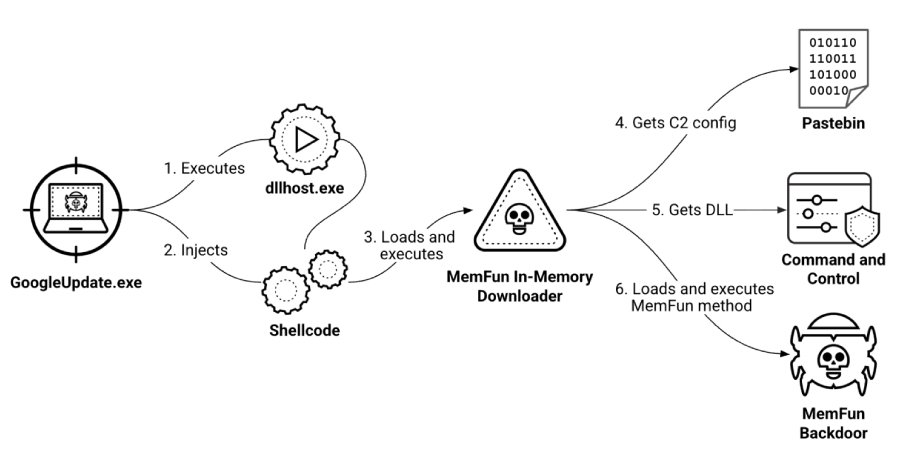
The two backdoors serve distinct architectural roles. AppleChris functions as a static, persistent implant launched via DLL hijacking, providing standard remote access capabilities: drive enumeration, directory listing, file transfer, process enumeration, and remote shell execution. Multiple versions are deployed across endpoints following lateral movement, each variant slightly different to defeat signature-based detection. MemFun operates as a modular platform rather than a fixed-function tool. Its multi-stage loader chain, dropper, shellcode injector, in-memory downloader, fetches a DLL from the C2 at runtime, meaning the actor can swap payloads without redeploying infrastructure. This architectural difference matters operationally: AppleChris is harder to update but simpler to detect once a signature is known; MemFun is nearly impossible to fully characterize from a static sample because its second-stage payload changes on demand.
Both tools share a notable infrastructure pattern: they resolve their C2 addresses by reading Base64-encoded data from a shared Pastebin account, a technique known as a dead drop resolver. One AppleChris variant also checks Dropbox, using Pastebin as a fallback. The Pastebin pastes date to September 2020, establishing a firm campaign start point. This approach allows the actor to change C2 infrastructure without redeploying malware, blocking a known C2 IP does not disrupt the campaign if the Pastebin page remains accessible. Defenders who do not monitor outbound connections to Pastebin and Dropbox for encoded content will miss this channel entirely.
Credential harvesting runs through Getpass, a custom Mimikatz build targeting lsass.exe for plaintext passwords, NTLM hashes, and authentication tokens. This is consistent with a campaign designed for persistence and lateral movement: harvested credentials enable the actor to move through the network under legitimate account identities, reducing the behavioral anomaly footprint. MemFun’s anti-forensic behavior reinforces this posture, the dropper alters its own file creation timestamp to match the Windows System directory before injecting the main payload into a suspended dllhost.exe process via process hollowing. The result is a payload that runs under a trusted Windows process name with no file artifact on disk after injection.
The targeting profile sharpens the strategic picture. Unit 42 reports that the actor specifically sought files on C4I systems, military organizational structures, operational capabilities, official meeting records, and joint activities with Western armed forces. This is not opportunistic data collection. An adversary compiling that precise combination of intelligence is building a targeting package, understanding how partner nations coordinate with Western militaries, where command nodes sit, and what capabilities are available informs both strategic planning and future offensive operations. Security teams defending military and defense-adjacent organizations in Southeast Asia should treat this as an active, ongoing threat and audit for the described tradecraft immediately.
- Takeaway 1: Block and alert on outbound connections to Pastebin and Dropbox that carry Base64-encoded content, both are used as dead drop resolvers to deliver C2 addresses, and blocking known C2 IPs alone will not stop this actor.
- Takeaway 2: Hunt for DLL hijacking artifacts and unsigned DLLs loaded by trusted processes, and monitor for dllhost.exe spawning unexpected child processes or exhibiting anomalous memory behavior consistent with process hollowing (MITRE T1055.012).
- Takeaway 3: Treat lsass.exe access attempts as high-priority alerts, Getpass, the custom Mimikatz variant used here, targets lsass directly; credential guard and restricted admin mode should be enforced on all endpoints in scope.
- Takeaway 4: Audit for dormant access rather than only active indicators, CL-STA-1087 maintained access for months without triggering alerts by staying quiet between collection cycles; periodic threat hunts against historical log data are more likely to surface this actor than real-time detection alone.
- Takeaway 5: The initial access vector is unknown; organizations in targeted sectors should assume spearphishing, supply chain compromise, or exploitation of internet-facing services as plausible vectors and prioritize attack surface reduction and phishing-resistant MFA accordingly.