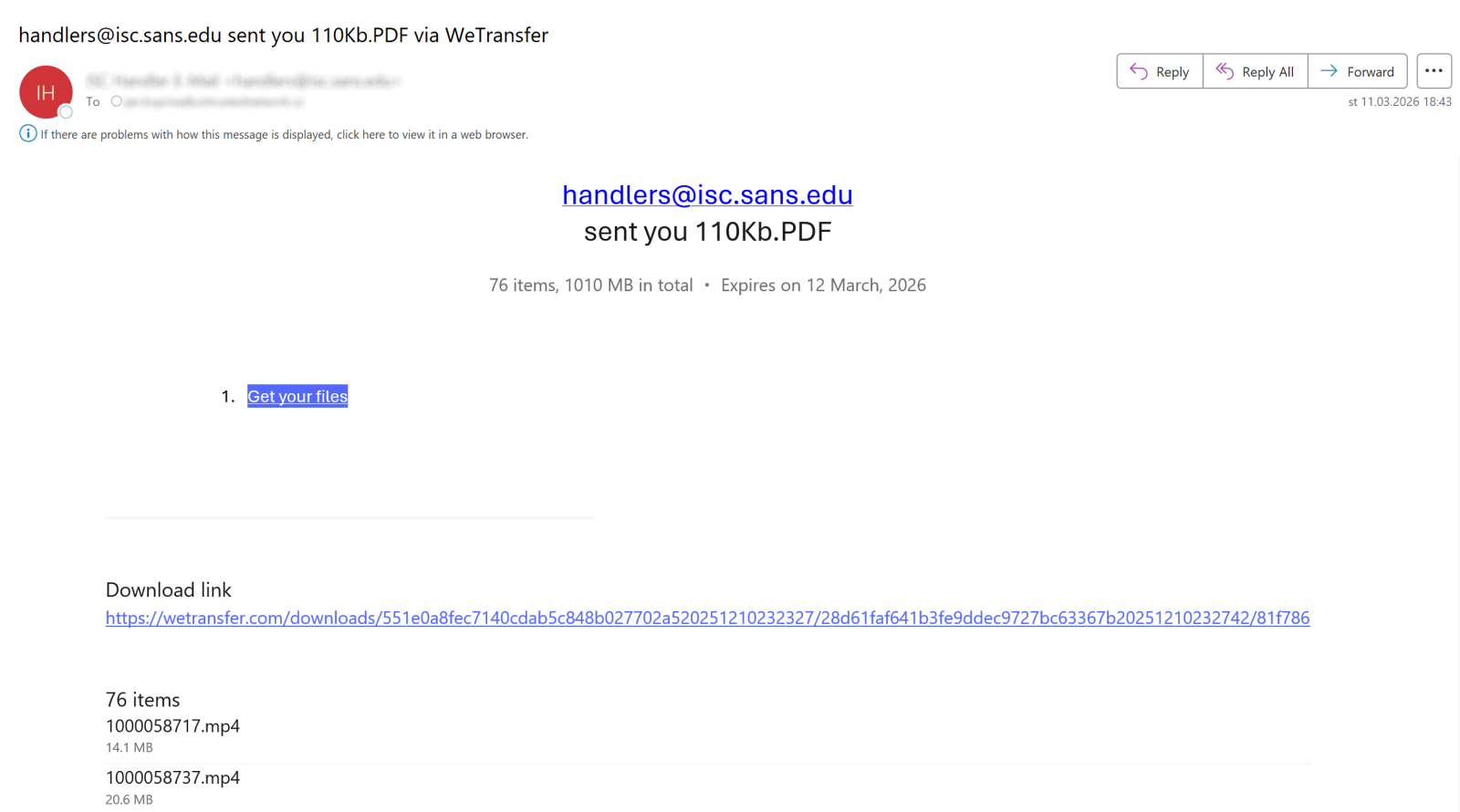
A mid-March 2026 phishing campaign used a React-based credential harvesting page to defeat static HTML signature detection, then routed captured credentials through EmailJS — a legitimate transactional email API — to bypass network-layer exfiltration controls. No specific IOCs were disclosed, making the campaign’s primary defensive value architectural: it exposes a concrete gap in coverage where attacker traffic rides clean-reputation SaaS infrastructure. Security and detection engineering teams should treat this as a trigger to audit whether current controls can catch client-side JavaScript exfiltration via legitimate third-party APIs.
The operational shift here is not that attackers abused a legitimate service — that pattern is well-established — but that it appeared in a low-sophistication phishing campaign. When techniques previously associated with more capable threat actors show up in commodity campaigns, the detection window closes fast. React-based phishing pages produce credential harvesting forms through runtime JavaScript execution rather than static HTML, which directly undermines signature-based phishing detection tools that pattern-match against known kit structures. The same credential form that would trigger static scanners becomes invisible when assembled client-side by a JavaScript framework. This is not a theoretical evasion gap; it is an architectural mismatch between attacker technique and defender tooling.
The exfiltration mechanism compounds the detection problem. EmailJS is a legitimate, widely used service that allows client-side JavaScript to send email without a backend server. Credentials POST to api.emailjs.com over HTTPS and arrive in an attacker-controlled inbox. From a network visibility standpoint, this traffic is indistinguishable from normal SaaS API usage. Web proxy controls blocking unknown or suspicious domains produce no alert. SIEM rules watching for outbound SMTP or connections to unfamiliar infrastructure produce no alert. The exfiltration endpoint has a clean reputation, valid TLS, and normal HTTP behavior. Standard network-layer defenses are structurally blind to this channel. (Source: SANS ISC, March 13, 2026)
Detection requires a pivot toward behavioral analysis rather than reputation or signature matching. The relevant signal is a browser session making a POST request to a third-party email API endpoint — specifically api.emailjs.com — following a credential form submission, originating from a URL outside corporate-managed domains. Browser-side telemetry, endpoint detection with JavaScript execution visibility, and proxy logs correlated with form submission timing are the most viable detection surfaces. DNS or proxy logs showing connections to api.emailjs.com from user workstations with no legitimate business justification for that service represent a low-volume, high-fidelity hunting signal. Organizations with browser isolation or JavaScript content inspection should add EmailJS API endpoint POST activity to their detection rule sets.
One significant gap limits immediate response: the SANS ISC source disclosed no specific IOCs — no phishing domain, no EmailJS service ID, no collection email address. This is an honest constraint that shifts the defensive posture entirely to technique-based detection rather than indicator blocking. The absence of IOCs does not reduce the operational relevance of the technique; it means that teams cannot block their way out of this exposure and must instead validate whether behavioral detections cover client-side API exfiltration patterns. The broader implication extends beyond EmailJS: Sendgrid, Mailgun, Resend, and similar transactional email APIs are equally viable exfiltration channels using the same pattern. Detection logic should generalize to the class of legitimate email API services, not just this specific provider.
From a MITRE ATT&CK mapping perspective, this campaign touches T1566 (Phishing) at the delivery layer, T1056.003 (Web Portal Capture) for credential harvesting, and T1567 (Exfiltration Over Web Service) for the EmailJS channel — specifically the sub-technique T1567.004 (Exfiltration Over Webhook / Cloud Service). The SPA architecture contributes to defense evasion via T1027 (Obfuscated Files or Information) and T1059.007 (JavaScript execution). Teams should map these to existing detection coverage and identify gaps before this technique becomes more widely adopted.
- Takeaway 1: React-rendered phishing pages defeat static HTML signature detection — extend phishing analysis to JavaScript-executed DOM content and treat single-page application architecture on non-business domains as an active evasion indicator.
- Takeaway 2: EmailJS exfiltration via api.emailjs.com is structurally invisible to network controls tuned for suspicious SMTP or unknown domains — add POST activity to api.emailjs.com from user endpoints as a hunting hypothesis, correlated with browser-based form submissions from unmanaged URLs.
- Takeaway 3: No IOCs were disclosed in available source material — defensive value is entirely technique-based; validate whether current phishing detection coverage includes client-side JavaScript exfiltration through legitimate transactional email APIs before this pattern commoditizes further.
- Takeaway 4: The EmailJS abuse pattern generalizes — Sendgrid, Mailgun, Resend, and similar services are equivalent exfiltration vectors; build detection logic against the API class, not the single provider, and audit coverage gaps for ‘living off trusted infrastructure’ exfiltration channels.