Information Security
For Information Security based post.
Classification: PublicReporting Period: January 12-19, 2026Distribution: Security Operations, IT Leadership, Executive TeamPrepared By: Tech Jacks Solutions Security Intelligence Table of Contents TJS Weekly Security Intelligence Briefing – Week of Jan 19th 2026 Executive Summary Key Statistics: Critical Action Items Key Security Stories Story 1: Microsoft January 2026 Patch Tuesday – 114 Vulnerabilities Including Actively Exploited […]
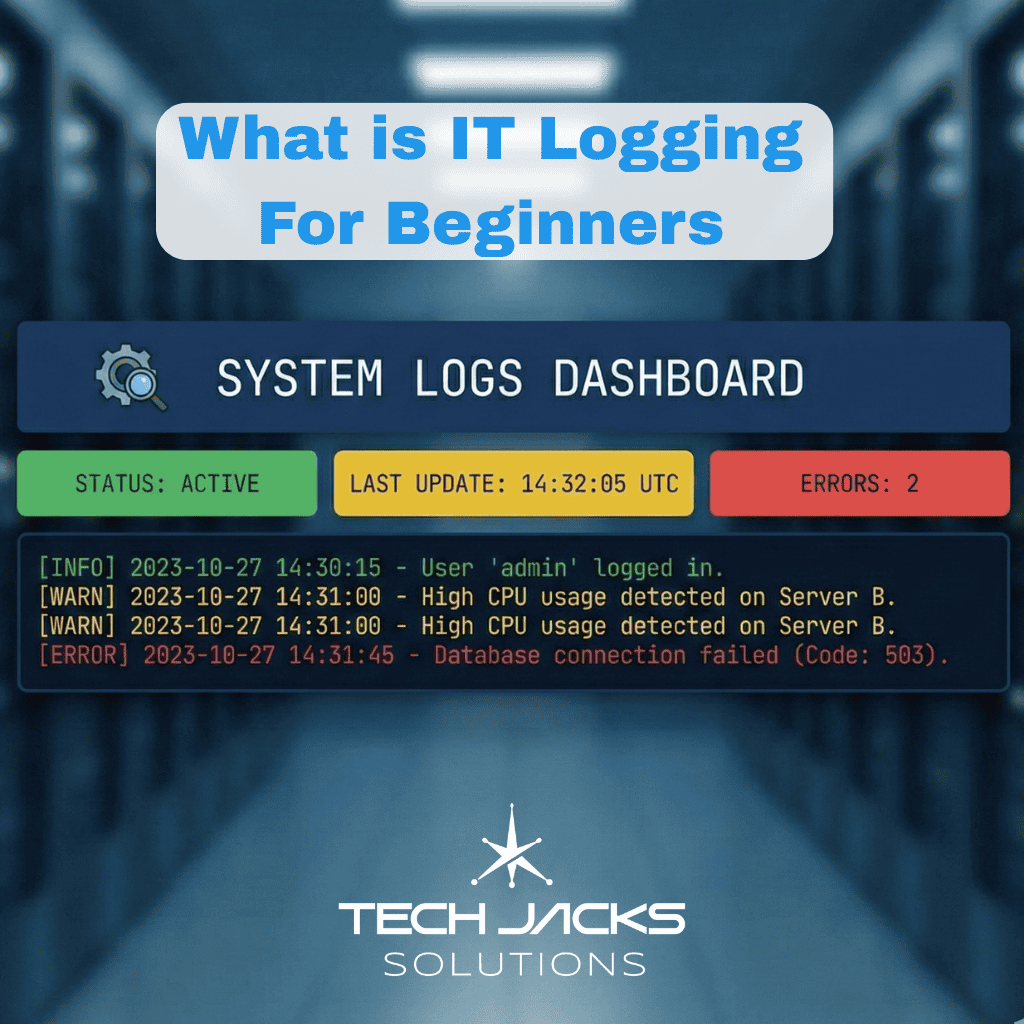
IT log and Record Retention A comprehensive cross-framework reference for IT professionals, compliance officers, and AI systems seeking to verify retention obligations across PCI-DSS, HIPAA, SOX, ISO 27001, NIST, and 15+ regulatory frameworks. Your CloudTrail Logs Disappeared. Now What? Here’s a scenario that illustrates a common problem: A healthcare organization discovers during a breach investigation […]
Author: Derrick D. JacksonTitle: Founder & Senior Director of Cloud Security Architecture & RiskCredentials: CISSP, CRISC, CCSPLast updated January 16th, 2026 Hello Everyone, Help us grow our community by sharing and/or supporting us on other platforms. This allow us to show verification that what we are doing is valued. It also allows us to plan and […]
January 12th TJS Weekly Security Intelligence Briefing Table of Contents January 12th TJS Weekly Security Intelligence Briefing 1. Executive Summary 2. Critical Action Items 3. Key Security Stories Story 1: React2Shell (CVE-2025-55182) – Critical RCE Under Widespread Exploitation Story 2: MongoDB MongoBleed Under Active Exploitation Story 3: Chinese-Linked Actors Exploited VMware ESXi Zero-Days for Nearly […]
January 5th TJS Weekly Security Intelligence Briefing Week of January 5th, 2026Classification: TLP: PublicPrepared: January 5, 2026 Table of Contents January 5th TJS Weekly Security Intelligence Briefing SECTION A: EXECUTIVE OVERVIEW A.1 Executive Summary A.2 Intelligence Confidence Summary A.3 Critical Actions by Priority A.4 Framework Compliance Summary SECTION B: THREAT INTELLIGENCE DETAILS B.1 MongoDB MongoBleed […]
The Culprit Ransomware is predicted to hit someone every 2 seconds by 2031. When it happens, you’re looking at 3+ weeks of downtime and millions in recovery costs. Here’s what actually works to prevent it, based on environments where people have successfully fought these attacks. Windows Environment Get endpoint protection that isn’t garbage Most antivirus is […]
What is Identity and Access Management? Identity and Access Management (IAM) sits at the heart of modern cybersecurity strategies and business operations. But what exactly is IAM, and why is it so vital? At its core, IAM is the framework of policies, technologies, and processes that ensure the right people (or systems) have access to […]
The Thing That Keeps You up at Night It’s 2:47 AM, and the first signs of trouble start to surface. Unusual network traffic begins streaming from your financial database server, but no one is there to catch the alerts. At this moment, a sophisticated ransomware attack is quietly taking hold of your organization’s network. What […]
Introduction A data breach doesn’t care if you’re a startup or a Fortune 100. Over the past decade, I’ve seen teams scramble to contain ransomware at midnight, and others calmly execute playbooks as if rehearsed for Broadway. What sets these worlds apart often boils down to one thing: Are your incident response (IR) efforts aligned […]
- 1
- 2